Hello Guys
welcome back again now the final touch to our ldap server and its auth.but before that let me refer to my previous blog explaining the setup of ldap server.
I will assume that you have gone through my previous blog and setup your own LDAp server with basic config so lets move ahead
welcome back again now the final touch to our ldap server and its auth.but before that let me refer to my previous blog explaining the setup of ldap server.
I will assume that you have gone through my previous blog and setup your own LDAp server with basic config so lets move ahead
Install Client Packages
On the client machine, you will needs to install a few packages to make authentication function correctly with an LDAP server.
You can install them from the default Ubuntu repositories with the following commands:
sudo apt-get update
sudo apt-get install libpam-ldap nscd
You will be asked a variety of questions similar to the those asked when you were installing the server components.
- LDAP server Uniform Resource Identifier: ldap://LDAP-server-IP-Address
- Change the initial string from "ldapi:///" to "ldap://" before inputing your server's information
- Distinguished name of the search base:
- This should match the value you put in your LDAP server's
/etc/phpldapadmin/config.phpfile. - Search for: " 'server','base',array " within the file.
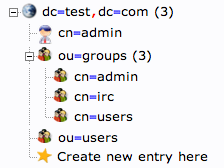
- Our example was "dc=test,dc=com"
- This should match the value you put in your LDAP server's
- LDAP version to use: 3
- Make local root Database admin: Yes
- Does the LDAP database require login? No
- LDAP account for root:
- This should also match the value in your
/etc/phpldapadmin/config.php. - Search for: " 'login','bind_id' " within the file
- Our example was "cn=admin,dc=test,dc=com"
- This should also match the value in your
- LDAP root account password: Your-LDAP-root-password
If you make a mistake and need to change a value, you can go through the menu again by issuing this command:
sudo dpkg-reconfigure ldap-auth-config
Configure Client Software
We have to adjust a few files to tell our authentication files that they can look to our LDAP server for authentication information.
First, edit the
/etc/nsswitch.conf file. This will allow us to specify that the LDAP credentials should be modified when users issue authentication change commands.sudo nano /etc/nsswitch.conf
The three lines we are interested in are the "passwd", "group", and "shadow" definitions. Modify them to look like this:
passwd: ldap compat group: ldap compat shadow: ldap compat
Next, we will add a value to our PAM configuration.
PAM, or Pluggable Authentication Modules, is a system that connects applications that can provide authentication to applications that require authentication.
PAM is already implemented on most computers, and works behind the scenes without needing user interaction. When we installed and configured our LDAP PAM module, most of the needed information was added to the configuration files.
Edit the
/etc/pam.d/common-session file:sudo nano /etc/pam.d/common-session
Add a line to the bottom of the configuration that reads:
session required pam_mkhomedir.so skel=/etc/skel umask=0022
This will create a home directory on the client machine when an LDAP user logs in who does not have a home directory.
We have to restart a service for these changes to be implemented:
sudo /etc/init.d/nscd restart
Permissions
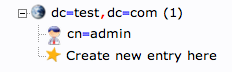
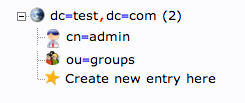
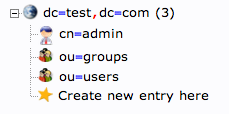
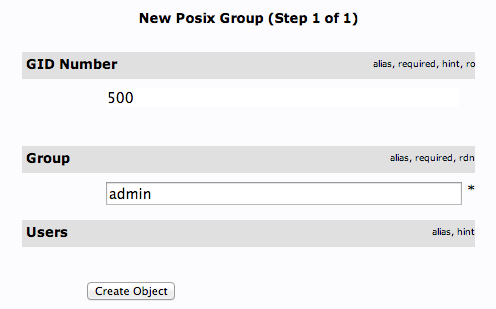
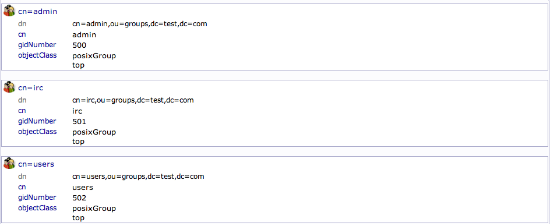
During the LDAP server configuration, we created a group called "admin". This was not chosen at random. It coincides with the "admin" group that is created by default on Ubuntu machines.
The LDAP users that you added to the "admin" group will have access to the
sudo command.
This is because we have a line that gives members of the "admin" group sudo access within the
/etc/sudoers file. Edit the file by issuing this command:sudo visudo
There is a line that reads:
%admin ALL=(ALL) ALL
Entries that begin with a percentage sign (%) specify a group instead of a user. If you wish to disable this functionality, or only grant specific users this functionality, comment out this line:
#%admin ALL=(ALL) ALL
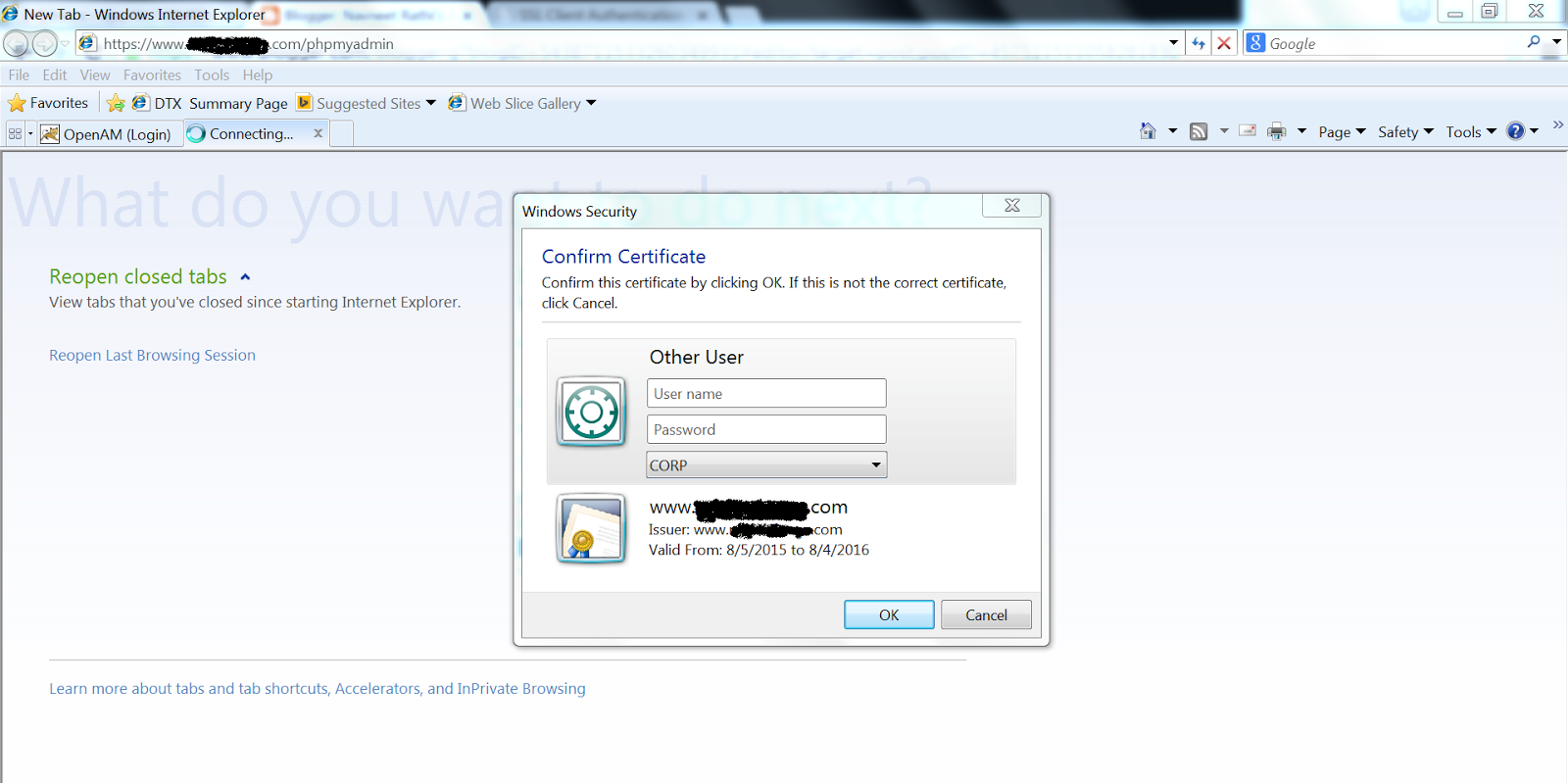
Log In as an LDAP User
We have now configured our client machine enough to be able to log in as one of our LDAP users. This user does not have to exist on the client machine.
In a new terminal window (it is best to keep your original terminal window logged in, in case of a configuration mistake), ssh into the client machine using an LDAP user's credentials:
ssh LDAP_user@LDAP_client_IP_Address
You should be able to log in as if your user had been created locally. Issue the print working directory command:
pwd
You should see that the home directory you selected for your user on the LDAP server is being used on this machine. It has been created on-demand to serve the LDAP user.
If you log out and log in with a different LDAP user, you can see that there will be two home directory entries:
ls /home
user1 user2
If your user is part of the "admin" group and you didn't disable the ability in the previous section, you will have normal sudo access, otherwise, you will not.
If you issue the
passwd command to change your password, you can see that it will be modifying your LDAP credentials:passwd
Enter login(LDAP) password:
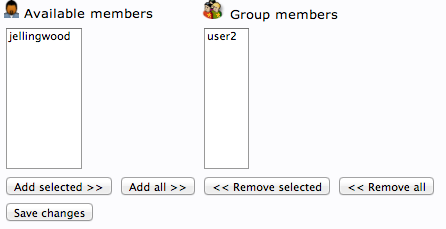
Restricting Access by Group
If you only want members of certain groups to be able to log into this specific machine, you can configure that restriction within the PAM files.
Edit the following file with root privileges:
sudo nano /etc/pam.d/common-auth
At the bottom, we will specify that PAM should look at the security access file to see how to restrict user logins. Add this to the bottom:
auth required pam_access.so
Save and close the file.
The file that PAM references for security information when that setting is configured is at
/etc/security/access.conf. Open this file now, with root privileges:sudo nano /etc/security/access.conf
We need to add a rule to the end of the file.
The dash (-) at the beginning of the line means this is a restriction. From the first colon (:) to the next colon, we specify who this rule applies to.
We specify that this applies to all users except root and the group "admin". Groups are given within parentheses.
From the second colon to the end of the line, we will specify under which circumstances the rule should apply. In our case, the restriction will apply in all circumstances but local logins.
-:ALL EXCEPT root (admin):ALL EXCEPT LOCAL
This will allow us to restrict logins to the "admin" group. We can add other groups or change the group.
This will also allow us to log in through the "console access" button on the DigitalOcean console if we somehow lock ourselves out of SSH.
Keep in mind that this will apply to all users, not just LDAP users. So any users you create on the client machine will need to be a member of one of the specified groups